
WaTTS is a Token Translation Service developed by KIT in the context of the INDIGO Data Cloud project. WaTTS was developed to address the users' need to access services that do not directly utilise federated access and require that the users use security tokens, such as SSH keys, X.509 ertificates, S3 access tokens etc. In this AARC pilot, WaTTS is integrated with the EGI CheckIn service, so that users can access WaTTS using their EGI accounts, while authenticating either at their home organisations or using their socialIDs. With WaTTS, users are able to manage the SSH access to a number of trusted VMs from a single point in a secure and user-friendly manner. In this pilot, WaTTS is used to manage their SSH public keys and provision them on demand to an authorised set of VMs. Although in this pilot WaTTS is integrated with the EGI CheckIn service, the solution is not limited to EGI, and can be used at any community/infrastructure/service where there is a need to "bridge" between different technologies, and can be run as a standalone "plug-and-play" solution. The only requirement is that the community/infrastructure/service supports integration of OIDC services.
Detailed description
Goal of the pilot is to demonstrate how the credentials can be managed according to user's identity. From the research/user point of view, the desired behavior is having an SSH access to desired VMs. From the administrator/coordinator point of view, the desired outcome is providing access to users in a straightforward manner, as easy as user uploading it's SSH key. However, such access should be granted only to authorized users. Therefore, LoA discrimination is used.
Pilot example is following:
The pilot structure is shown in picture below.

The pilot authentication flow is shown below:
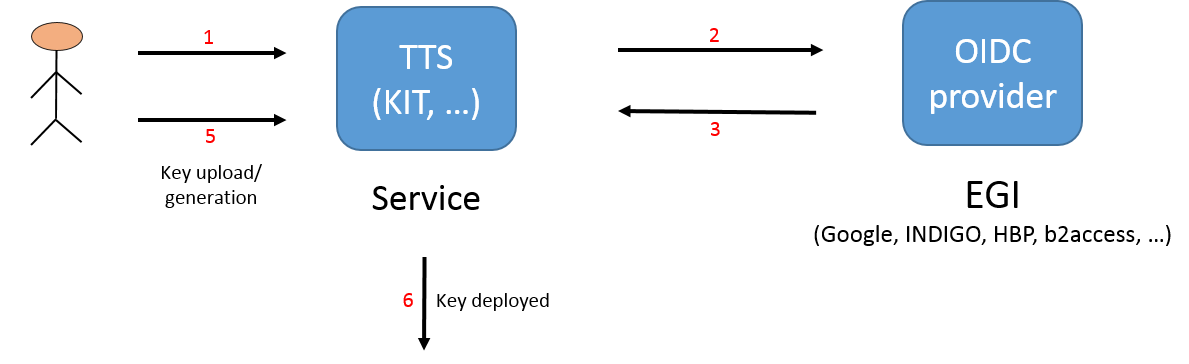
It is important to mention that at neither step the credentials (in this case SSH keys) are stored on the WATTS service.
WaTTS is actively maintained and it is running in production. As already mentioned, it is not limited to EGI OIDC providers, but already supports Human Brain Project (HBP), b2access, Google, and naturally, INDIGO IAM (INDIGO Access Management). Adding additional IdPs or configuring the service is straightforward. Support for additional credentials is done through plugins, for which the API is defined, and can therefore be developed as needed.
WATTS source and info pages:
https://github.com/indigo-dc/tts
https://www.gitbook.com/book/indigo-dc/token-translation-service
Note that page might be moved in the future to https://github.com/watts-kit/watts.
| Pilot resources | |||
|---|---|---|---|
WATTS service (https://watts-dev.data.kit.edu) - development version | |||
EGI CheckIn service | |||
2 VMS provided by ~okeanos. | |||
| KIT Grid certificate (used to authenticate with EGI CheckIn service), alternatively Google account is used, however LoA connected with Google account is not sufficient to upload keys (this is by design, it is configurable, naturally) |
Demonstration workflow
| Access to the cloud resources | ||
|---|---|---|
| 1. | Access WaTTS instance at https://watts-dev.data.kit.edu Select "European Grid Infrastructure" and click on "Login".
|  |
| 2. | Select your Identity Provider from the discovery page (WAYF). The institutional IdP to select (for this demo) is: IGTF Certificate Proxy, and then we use the institutional grid certificate (in this case, KIT Grid Certificate) |  |
| 3. | This page displays which values will be released by IGTF-to-eduGAIN-Proxy. User should click on Yes to accept and proceed.
|  |
| 4. | This page displays which values will be released by EGI-CheckIn. User should click on Yes to accept and proceed. We can see that the LoA is now Substantial. |  |
| 5. | Upon successful login, the user is redirected to the WaTTS. We then select the desired plugin, in this case aarc_ssh, and we can select either Request, or Advanced. First option creates SSH key par for the user, and deploys the public key to the VMs. User then must download the key pair if intends to use them, since the keys are never stored on WaTTS. If skipping this step, user must recreate the SSH keys again. Second option (Advanced) will enable the user to upload its own public SSH key. |  |
| 6. | If user select Advanced option, then it is able to upload its own key. After pasting the key, user should click on the Submit button.
|  |
| 7. | After successfully uploading or generating SSH key, the user now has SSH access to VMs. The username and full VM hostname is displayed to the user. | |