Requirement
|
Overview
In the previous article we enabled and checked IPv4 connectivity between all potential host within 192.168.128.0/17 and the outside Networks beyond ISP box. But, this is pretty useless as I can't imagine my kids typing IPv6 address (2001:8b0:0:30::666:102) in the browser in order to play a FUN puzzle. (Though for now we are suppose to have only IPv4 ) So we definitely need to provide name service resolution at the SOHO router itself.
Article objective
In this article we will pursue the SOHO network appliance installation and enable name service to all host @ home.
Diagrams
[ SOHO #005 ] - "Got your Id number, but ... What's your name ?"
Verification
Conclusion
In this article DNS service has been enabled at:
- SOHO router level
- All host getting an IPv4 via DHCP will get a DNS server set to SOHO@loopback0 (192.168.254.1)
RARE validated design: [ SOHO #005 ] - key take-away
In this example the key take-away are:
- proxy-profile usage in order to proxy DNS query into VRF inet
- proxy-profile can be used to proxy other types of traffic
- data/routed traffic is not affected by proxy-profile
Requirement
|
Overview
In the previous article we enabled and checked IPv4 connectivity between RARE/freeRouter and ISP box using sdn1 interface within 192.168.0.0/24 network. But as stated in the previous post, I'd like:
- all people connected within 192.168.128.0/17
- to access the external world
Article objective
In this article we will pursue the SOHO network appliance installation and enable IPv4 connectivity for all host connected within your internal network to the external world.
Diagrams
[ #004 ] - Do you need translation ?
IPv6 does need NAT in my specific case as my ISP has allocated me public IPv6 prefixes. We will see IPv6 configuration in the next articles.
Verification
Conclusion
In this article
- We finally have a router that enables connectivity for all hosts inside the home network to the outside world
- due to the ISP specific setup, our router had to translate inner home IP subnets to subnet that can be in turn NAT'ed by the ISP box.
- We have a consistent IPv4 addressing plan
- We now can add very exciting feature from now on. (In next articles !)
RARE validated design: [ SOHO #004 ] - key take-away
In this example we are proposing a basic connectivity scenario. However, keep in mind that depending on your location the configuration might be drastically different. But do not fear ! RARE/freeRouter has all the features need to enable connectivity !
- NAT64 is available. So in case you want to run a pure IPv6 network, freeRouter can NAT64 traffic for you.
- NAT46 is also available. In case you are desperate and don't want to implement a pure IPv6 home network and have an ISP running only IPv6, freeRouter can NAT46 your traffic for you !
- In the example described, we are lucky to have IPv6 public global IPv6 address. We will see IPv6 configuration in subsequent articles.
Requirement
|
Overview
When installing RARE/freeRouter on x86, you have 2 choices:
- installation with a software dataplane
- installation with a DPDK dataplane
In this precise case, we will consider a DPDK dataplane installation as our hardware is compliant to the requirement listed below.
DPDK requirements
- CPU with SSE4 support
- DPDK compatible NIC
Note that freeRouter is available where JVM is available
- x86
- ARM
Article objective
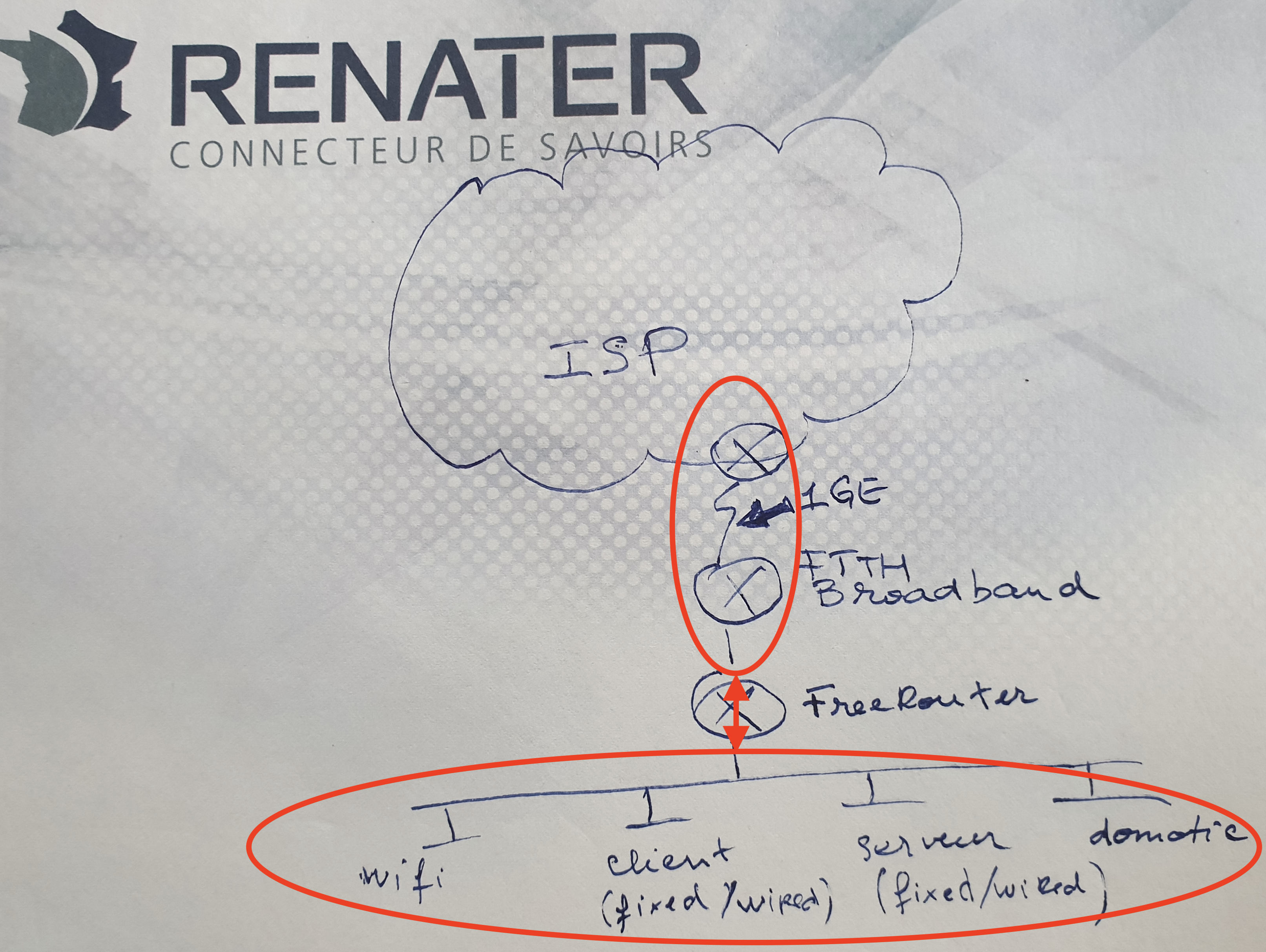
In this article we will pursue the SOHO network appliance installation based on the diagram below, and freeRouter installation using DPDK dataplane. In this situation, the appliance is behind ISP FTTH box demarcation point. As it is typical to French FTTH domestic deployment.
Deployment consideration
In this case, RARE/freeRouter is connected to a ISP box demarcation point that deliver copper connectivity. Nothing prevents you, following your context, to deploy a similar equipment with with SFP uplinks directly connected to your Provider Edge backbone routers if you own also the dark fiber paths local to the MAN.
Diagrams
[ #003 ] - RARE/freeRouter DPDK SOHO installation
IPv6 addressing plan has not been forgotten. It is not mentioned here on purpose in order to not complicate explanations. IPv6 we be the object of further articles. It is not that IPv6 is a complex topic. It just that it deserves special attention. You might not realised it, but IPv6 is everywhere and is used by default between peers as soon as IPv6 is enable. So IMHO we need to get used to it as soon as possible especially if you are a network administrator.
Verification
Conclusion
In this article
- we finally launched RARE/freeRouter with DPDK dataplane
- configure RARE/freeRouter with a vanilla config that takes into account all the appliance physical interfaces
- added veth pair in the config in order to take into account:
- Control plane / Data plane communication
- linux OOBM
- integrated WIFI
- Enabled and checked IPv4 connectivity between freeRouter@sdn1 and ISP demarcation point
- Check telnet access to freeRouter from localhost only
RARE validated design: [ SOHO #003 ] - key take-away
From this point you have a complete freeRouter connected to ISP box via SDN1 as uplink in 192.168.0.0/24 subnet. We will extend further this base configuration step by step in order to enrich user experience !
- Now you would want to enable IPv4/IPv6 connectivity to all potential hosts@home whether they are connected via RJ45 or via built-in WIFI.
- you would also want to distribute IPv4, IPv6 to all the of hosts@home
- IPv4/IPv6 connectivity is not enough, you would like to provide Domain Name Service to them
- Domain Name Service is not enough if they can't reach outside world. As we are using RFC1918 addressing plan we should figure out a way to ensure NAT/PAT address translation in order to enable egress traffic toward the Internet
- Your home might have several floors and only one WIFI access point is not enough ? Let's see how we can add additional WIFI AP in the network
- Maybe you have an outsourced network management service ? Let's see how connectivity can be enable via OpenVPN encrypted tunnel
- Last but not least, let's see how we can connect DN42 parallel network using a Wireguard tunnel relying on an IPv6 underlay.
You've guessed it, all of these points will be elaborated in the futures articles. Therefore stay tuned !
Requirement
|
Overview
I'm not sure if this is still the case now, but back in 1999, I had the opportunity to managed multiple VPNs at a very huge French Service Provider. I'm saying huge as in this type of MPLS muti-service core network, you could have hundreds of VRF in the same PE router connecting a myriads of CPE via X25 (XOT), frame-relay and ATM PVC at best. In that context, some companies could have several thousands of routers in their VPNs and it was not common to follow a high pace deployment which was at ~10 CPEs per day for a new customer VPN implementation. So one of my favorite CLI command was:
copy tftp run Address or name of remote host []? <x.y.z.t> Source filename []? <router-cpe-config-file-name> Destination filename [running-config]? ...
That being said, I'm not sure if this has evolved since then as TFTP occurred inside a very protected out of band management network, it was very good and did a perfect job. Keep in mind that we could be hundreds of "VPN owner" deploying CPEs at the same time. This has to be highly available.
That was for the anecdote, but recently I attempted to upgrade my OpenWRT wifi router from 18.06.02 to the latest code train: 19.07.4. As a I'm lazy, I just sticked with OpenWRT web upgrade via LuCI. Not sure if I was right ... I don't know why and how but the upgrade failed and my wifi router got "bricked".
After a lot of googling and reading, i concluded that I had only one solution: restore from factory and re-install OpenWRT 19.07.04 installation by hand. You have guess the rest of the article, the factory-reset procedure requires a TFTP server.
Note
But before that, I had to solder an USB - UART module as described here.
Article objective
As again i was lazy on installing a TFTP server on my MAC and disconnect my current LAN access in order to have a direct connectivity with the OpenWRT box, I had an idea (this is not often ) off the top of my head: "Hey, maybe freeRouter has a TFTP server that I can activate in few lines ?"... Well, after a terminal connection to my home router let me introduce you to freeRouter/TFTP server:
[ #004 ] - Saving private OpenWRT", thanks freeRouter's TFTP server !
Note
Discussion
You can deploy freeRouter manually in a VM or container and bind it to a linux interface if you need a TFTP server in order to apply configuration to all your equipment. When final staging are done in a secure Out of Band management network context having a TFTP server is a blessing as it correspond to a gain of time in a production environment. Imaging hundreds of people working in a SP environment and working at the same time.
Conclusion
In this 4th article:
- We presented freeRouter TFTP embedded server
- You can use it in order to undertake network equipment deployment requiring TFTP
- This TFTP server is compatible with IPv4/IPv6
TFTP is a basic but a common tool in SP environment (or it was? If it is still used, yes please confirm !) In this example, I demonstrated the use of TFTP server in order to flash a wifi router to factory default. I have 802.11ac back up and running !
Final words
freeRouter can be perceived not only as a router but it is a networking Swiss army knife. in further articles we will shed some lights in various treasures hidden into freeRouter... And for free !
Last but not least, you can play with these different servers from this sandbox: (You'll be able to spot amazing server that will be the object of further article.)
Trying 193.224.23.5... Connected to dl.nop.hu. Escape character is '^]'. XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX XXXX XXXXX XXX XXX XXX XX XX XXXX XXXXXXXXXXXXXXXXXXX XXXX XXXX XX XXXX XX XXXX XX XX XX XXXX XXXXX/~~~~~~\XXXXXX XXXX X XXX XX XXXX XX XXXX XX XX XX XXXX XXXX| player |XXXXX XXXX XX XX XX XXXX XX XXX XX XXXX XXXXX\______/XXXXXX XXXX XXX X XX XXXX XX XXXXXXX XX XX XXXX XXXXXXXXXXXXXXXXXXX XXXX XXXX XX XXXX XX XXXXXXX XX XX XXXX XXXXXXXXXXXXXXXXXXX XXXX XXXXX XXX XXX XXX XXX XX XXX XXXXXXXXXXXXXXXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX welcome line ready menu lab: # - reboot router1 $ - reboot router2 % - reboot router3 1 - connect to router1 2 - connect to router2 3 - connect to router3 ^ - rebuild routers l - connect to lg.nop.dn42 x - exit choose:1 - attach vdc lab1 welcome line ready yourname#conf t warning user.userLineHandler.doExec:userLine.java:606 <nobody> configuring from tty1 yourname(cfg)#server ? bmp2mrt - configure an bmp to mrt server bstun - configure a bstun server chargen - configure a chargen server daytime - configure a daytime server dcp - configure a dcp server dhcp4 - configure a dhcp4 server dhcp6 - configure a dhcp6 server discard - configure a discard server dns - configure a dns server echo - configure an echo server etherip - configure a etherip server forwarder - configure a forwarder server ftp - configure a ftp server geneve - configure a geneve server gopher - configure a gopher server gre - configure a gre server gtp - configure a gtp server honeypot - configure a honeypot server http - configure a http server irc - configure an irc server iscsi - configure an iscsi server l2f - configure a l2f server l2tp2 - configure a l2tp v2 server l2tp3 - configure a l2tp v3 server loadbalancer - configure a loadbalancer server lpd - configure a lpd server modem - configure a modem server mplsip - configure a mplsip server mplsudp - configure a mplsudp server multiplexer - configure a multiplexer server netflow - configure an netflow server nrpe - configure a nrpe server ntp - configure a ntp server openflow - configure an openflow server p4lang - configure an p4lang server pcep - configure a pcep server pckodtls - configure a pckodtls server pckotcp - configure a pckotcp server pckotxt - configure a pckotxt server pckoudp - configure a pckoudp server pop3 - configure a pop3 server pptp - configure a pptp server prometheus - configure a prometheus server quote - configure a quote server radius - configure a radius server rfb - configure a rfb server rpki - configure a rpki server sip - configure a sip server smtp - configure a smtp server snmp - configure a snmp server socks - configure a socks server streamingmdt - configure a streaming telemetry server stun - configure a stun server syslog - configure a syslog server tacacs - configure a tacacs server telnet - configure a telnet server tftp - configure a tftp server time - configure a time server udpfwd - configure an udp forwarder server udptn - configure an udptn server upnpfwd - configure an upnp forwarder server upnphub - configure an upnp hub server voice - configure a voice server vxlan - configure a vxlan server yourname(cfg)#server ...
In order to exit the sandbox session use the following escape sequence: Ctrl-c + Ctrl-x
Requirement
|
Overview
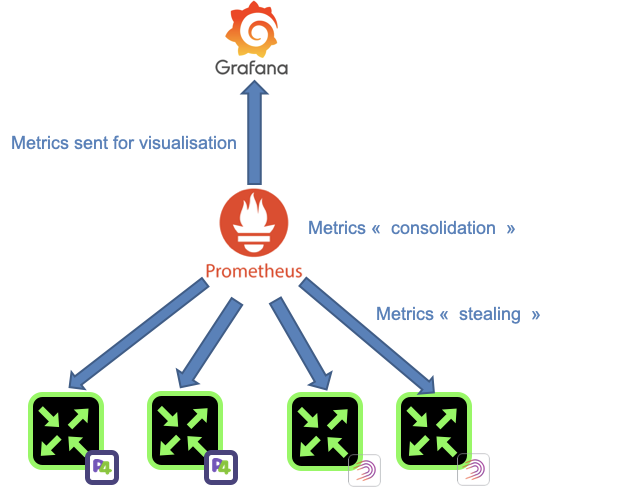
In Greek mythology, Prometheus is a Titan that is credited mankind creation by stealing Fire from Gods and by giving it to human. In the RARE context, Prometheus is a the software from prometheus.io project. It became very popular in the IT industry as it is very simple to implement/configure while providing a great number of metrics without impacting application performance. It is heavily used in microservices environment such as docker and Kubernetes. The mythological reference gives us an indication of how Prometheus is operating. At a constant rate, Prometheus metric collector or server is stealing metrics from Prometheus agent. All the stolen metrics are then consolidated in Time Series database ready to be poured to a queueing system for proper visualization.
Before going further, allow me a brief digression by sharing with you a small anecdote that leds to this ongoing work related to network monitoring for RARE. As mentioned previously, our focus is to elaborate RARE/freeRouter solution the possibility to be monitored in an operational environment. In that context, we started with the implementation of a lightweight SNMP stack that provided relevant result via SNMP tools like LibreNMS. This is great for organisation that wouldn’t want invest time on anything but SNMP.
However, we felt a lack of flexibility due to SNMP inherent structure and we needed more versatile and instant monitoring capabilities. More importantly the need to export infinite metric type from Control Plane in a more flexible way arise. How metrics such as: Number of IPv4/IPv6 routes, IPv4 BGP prefix, IPv6 BGP prefix platform JVM memory etc. could be shared without too much hassle ?
After some internal discussion, I just said: "I’m not a monitoring expert but we have tools like ELK and PROMETHEUS and GRAFANA in NMaaS catalog … Shouldn’t we consider use this ?"
The answer was: « Let’s give it a try and fire up a Prometheus and Grafana instance from NMaaS platform !»
Some hacking at the control plane code level were initiated, after few hours freeRouter lead developer came up with a solution and said: Let me introduce you "freeRouter prometheus agent »
And thanks to the great support of NMaaS team, in few minutes and some point and clicks (it took longer than expected as I’m not good with GUI) we were able to test this agent.
Why is it important you might say ? It is just that with prometheus simplicity and low resource overhead with have full control plane metrics visibility !
As a side note this is not a replacement for INT/Telemetry/Netflow/IPFIX that provide different type of data that are to at the same scale…
People with INT/TELEMETRY/NETFLOW/IPFIX are talking about a "data lake" or "data deluge". Which is correct, if you think about the complexity of resolving a gigantic producer/consumer data problem. This needs the relevant IT infrastructure in order to process all of the data provided by these protocol at the NREN scale.
While in our case, we are just focusing on exposing CONTROL PLANE METRICS at the network element level. We simply monitor and ensure a router operation by using prometheus metrics
Note
While he above might be true, the number of metrics exported from a prometheus target can be very high. Fine tuning might be necessary in order to make sure that all metrics are really necessary for network monitoring purpose. This explosion of metrics exposure can add unnecessary workload at the control plane level.
Again, kudos to NMaaS team that made this happen so that we could test this on the P4 LAB with — ZERO — effort.
Article objective
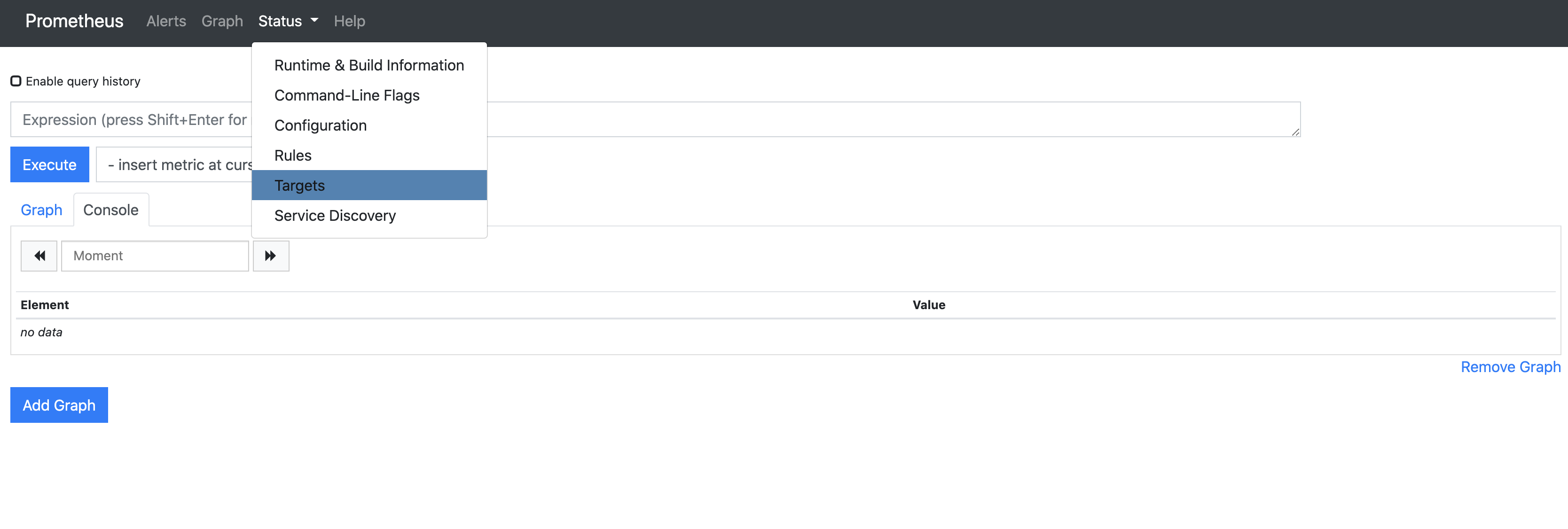
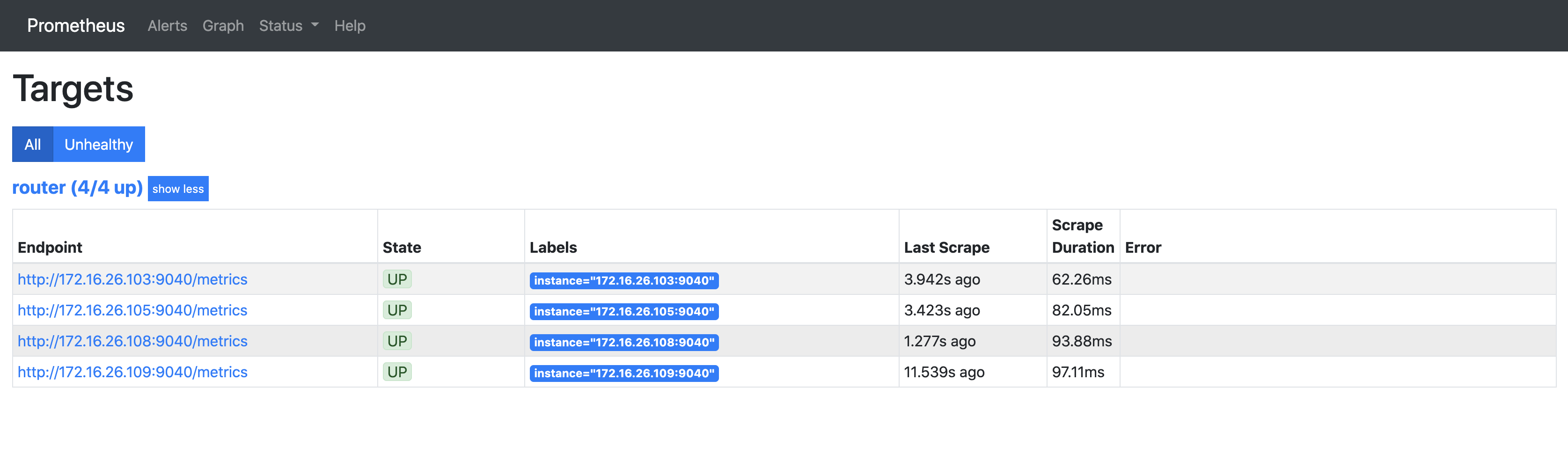
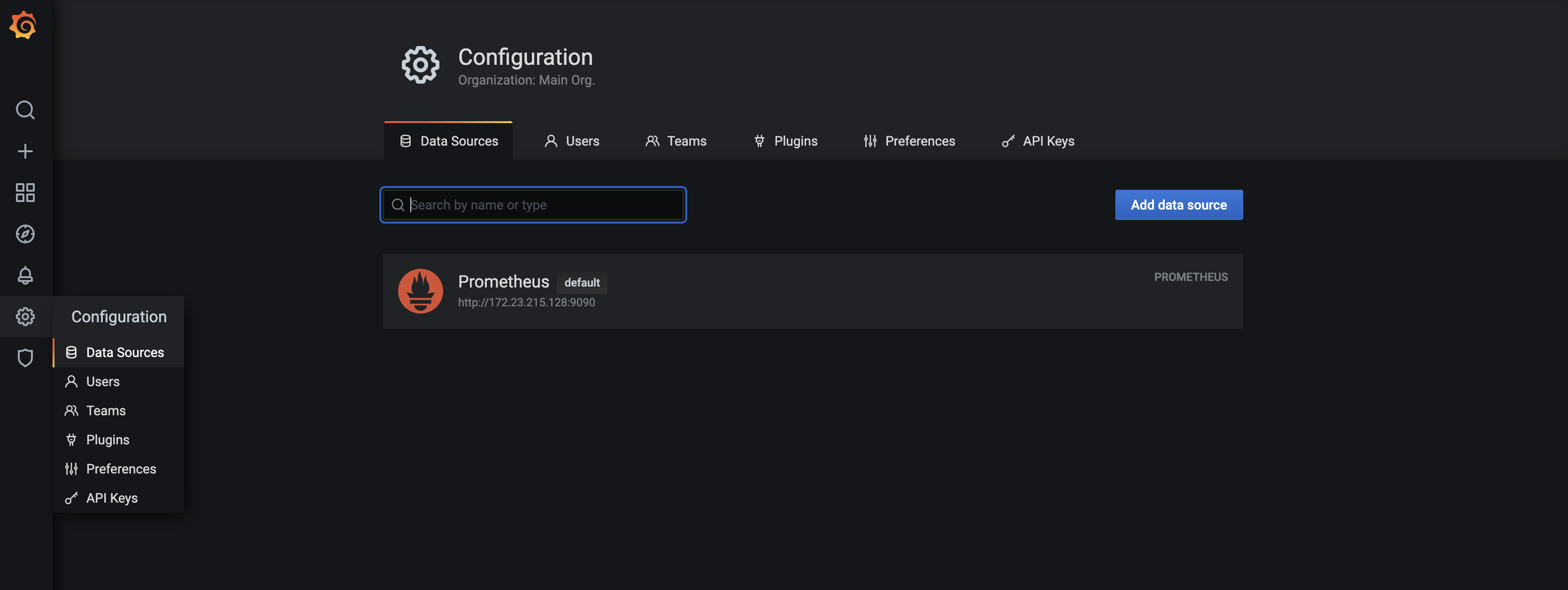
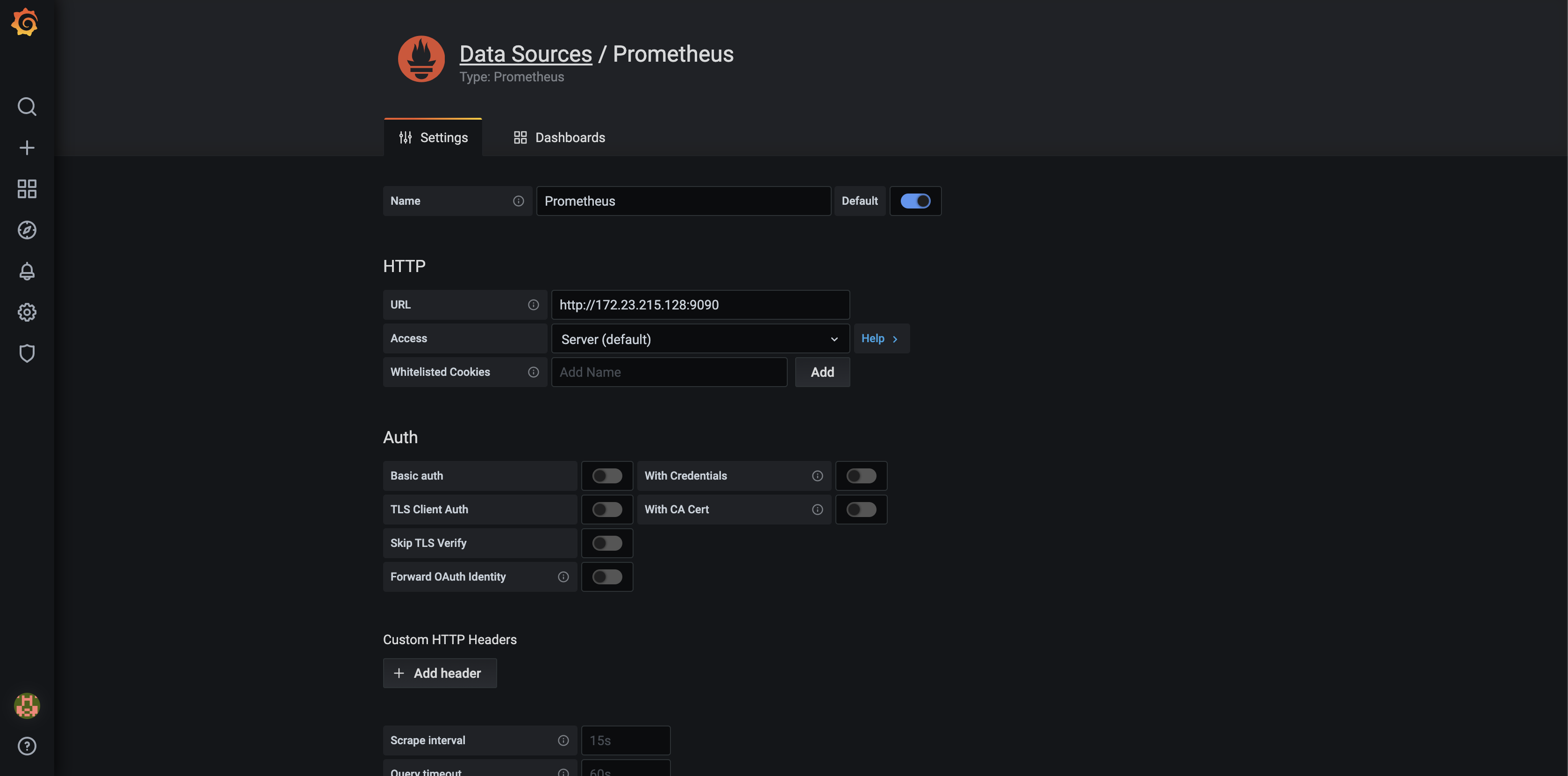
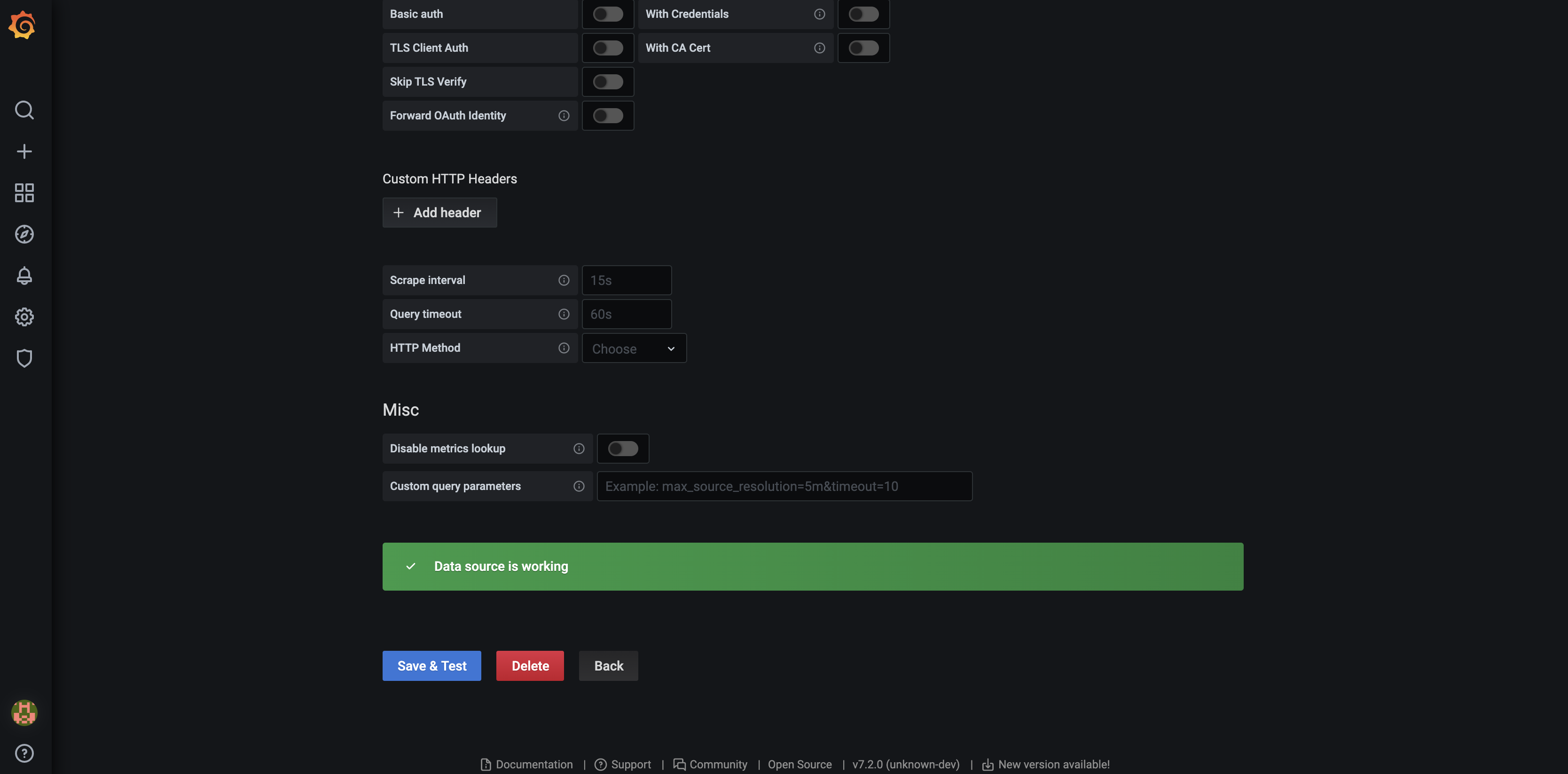
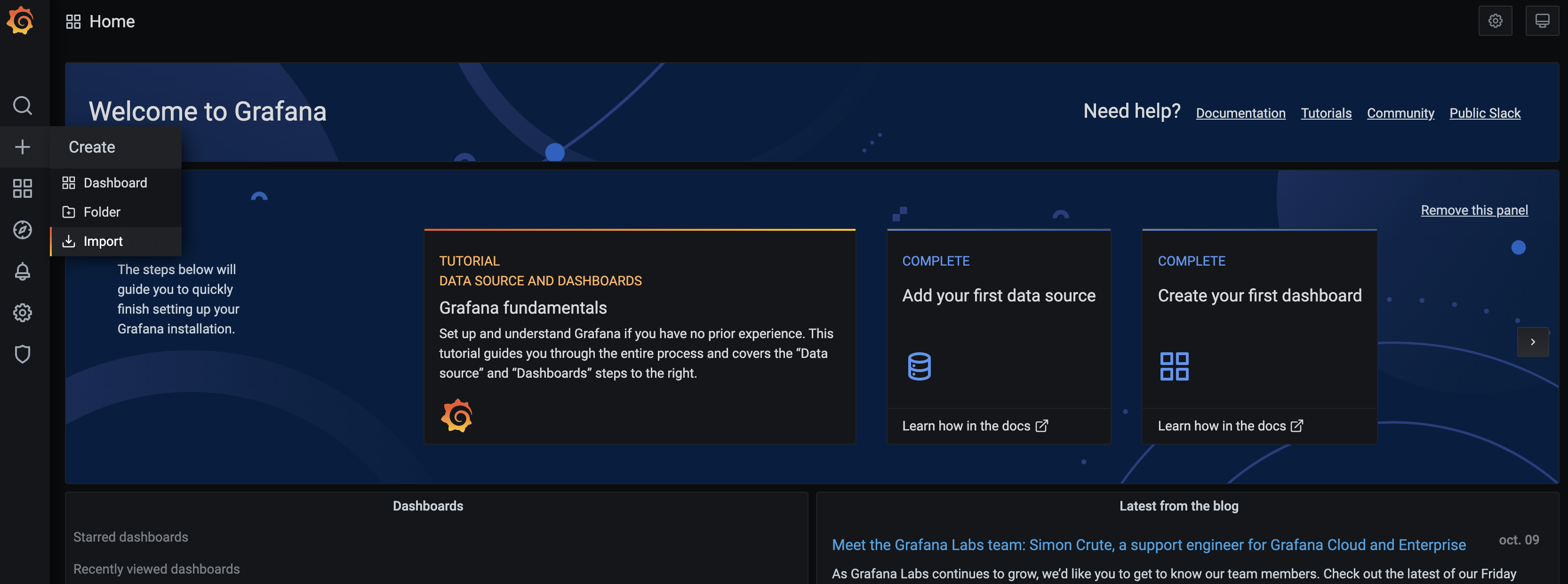
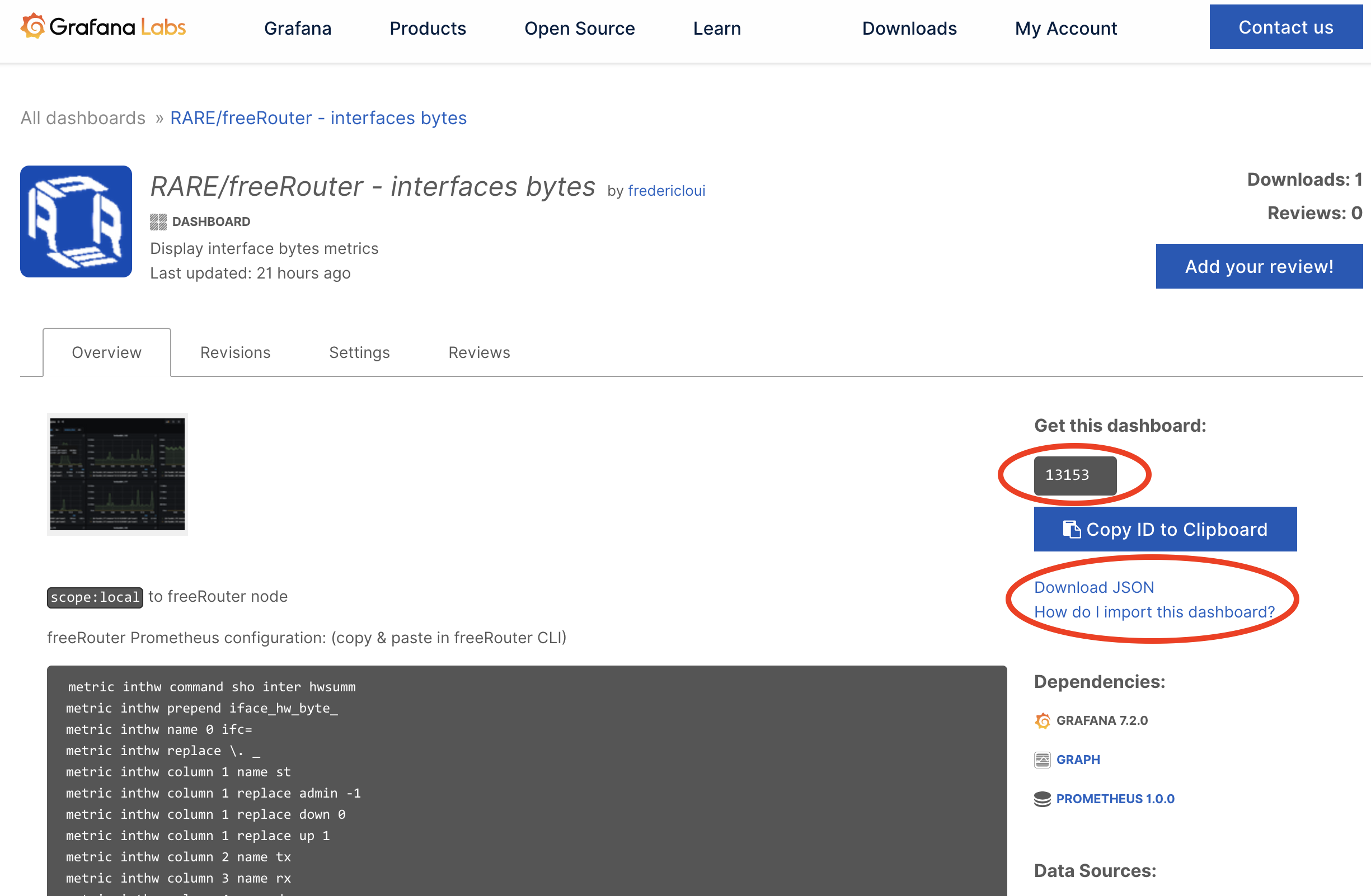
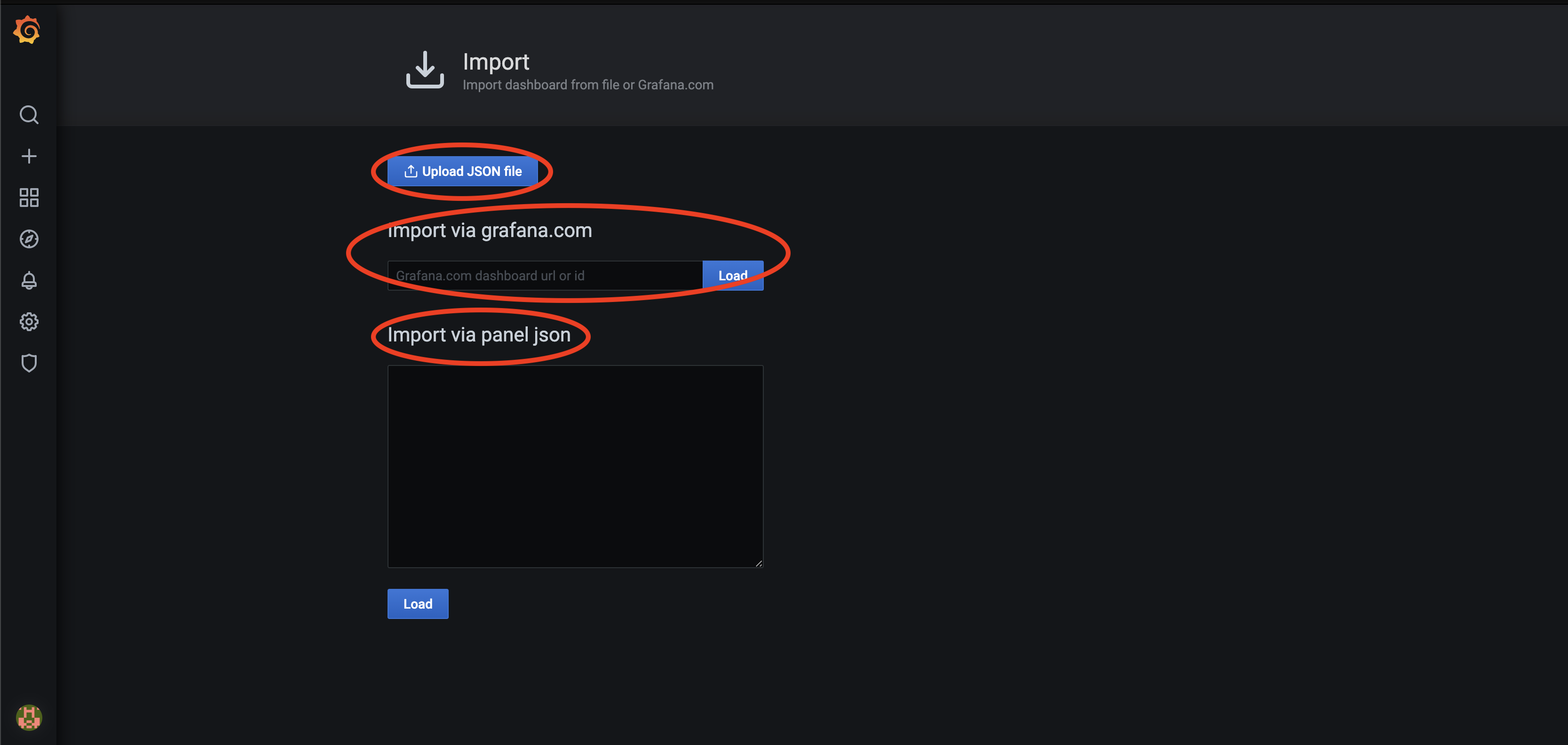
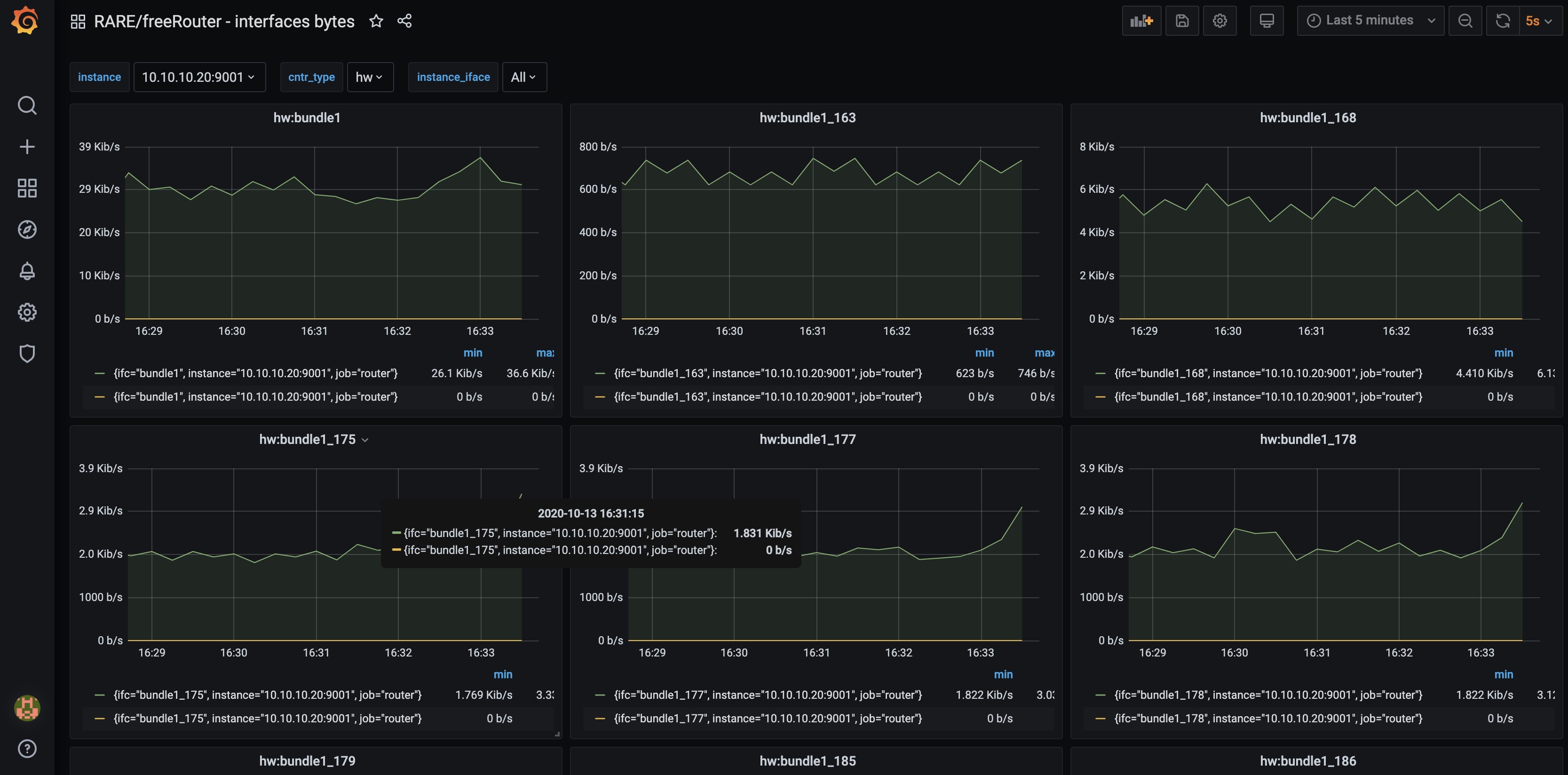
In this article, we will present freeRouter and Prometheus integration and as an example we will implement one of the 22 grafana dashboard that we developed and published here. In the rest of the article we will assume that you are a running one or more freeRouter nodes.
Diagram
[ #001 ] - Cookbook
Discussion
This example related to interface metrics is universal, as the metrics at freeRouter level are yielded through a generic CLI command:
- "show interface hwsummary"
- or "show interface swsummary".
However some metrics cannot be retrieved by generic interface. Some metrics will be tied to specificities of your network. These can be the AS number, IGP process name, VRF name etc.
Let me give you a couple of examples:
Conclusion
In this 1st article, you were presented :
- freeRouter/Prometheus integration
- How to add a new router in the list of Prometheus target
- How to integrate a RARE/freeRouter Grafana Dashboard. (Feel free to adapt the other available dashboard query to your context !)
Final words
In Prometheus philosophy, normally the user should do only the minimum of tweaking regarding configuration. Ultimately, he should be only be able to enable a metric or simply disable it if the scrape cost is too high. However in freeRouter/Prometheus integration process, you see that some metric are issued using specific $variable (VRF, BGP/IGP process number ...) Which makes impossible to maintain this universality. However, from the network operator point of view this should not be a showstopper. On the contrary, it is a powerful choice to be able to alter these command via $variables.
Remember in freeRouter philosophy you can have multiple VRF, multiple IGP and multiple BGP process number ! (Which is not the case for all routing platform)
Last but not least, this Prometheus agent was developed quickly because of one reason, all the objects at the control plane level were already well structured in table form as previously described in this article. So implementing this table row/column logic in order to derive a prometheus metric was technically possible without too much hassle.