Introduction
This pilot aims at demonstrating possible mechanisms to include Social Identities in the Authentication and Authorization process for providing federated access to resources within a given research collaboration, exploiting mechanisms to enhance the LoA of the users. The idea is to be able to support individual researchers that are not affiliated with any of the traditional home organisations, as well as those users whose Identity Providers are not part of any of the eduGAIN participating federations.
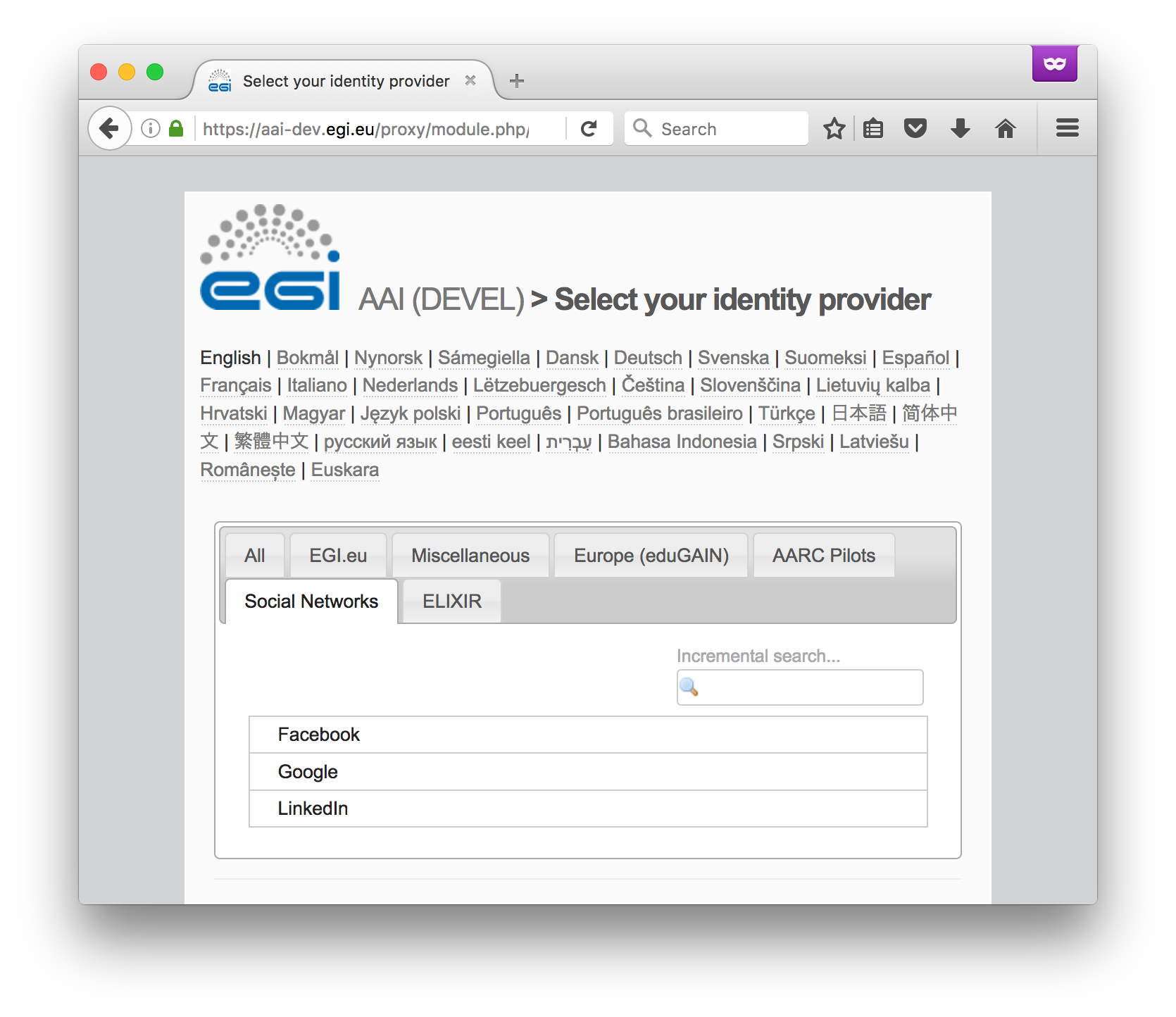
The pilot showcases how to cater for these cases by enabling a research collaboration, namely the AARC Pilot User Community, to use social networks as third party Identity Providers. The key factors in enabling such Guest Identity services is to be able to support multiple technologies and flexible policies in a scalable and trustworthy manner. In this context, the pilot is based on an SP-IdP proxy architecture (see also AARC Blueprint Architecture) through which users are able to authenticate with the credentials provided by the IdP of their Home Organisation (e.g. via eduGAIN), as well as using Social Identity providers, or other selected external identity providers. Specifically, the proxy has built-in support for SAML, OpenID Connect and OAuth2 providers and enables user logins through Facebook, Google, LinkedIn, and ORCID. The proxy is then responsible for enriching the identity information that comes from these external IdPs with additional attributes, including the following:
- a unique, persistent, non-reassignable user identifier (namely AARC ID, expressed as an
eduPersonUniqueIdattribute scoped at"@aarc-project.eu"); - assurance level (expressed as an
eduPersonAssuranceattribute); - community membership roles and groups (expressed through
eduPersonEntitlementattribute values).
Note that a user cannot access federated resources until they obtain an AARC ID through enrollment in the AARC Pilot User Community. In addition, we have defined a minimum set of attributes required for registering for an AARC ID. The SP-IdP proxy will attempt to retrieve these attributes from the user’s Home Organisation. If this is not possible, then the user will be asked to provide the missing attribute values and the request to join the collaboration will need to go through a verification process by the collaboration's Sponsors.
Demonstration portal
For the purpose of this pilot, we have enabled federated access to the dashboard of a demo OpenStack Cloud deployment. Specifically, the pilot IdP proxy has been configured to authenticate users and communicate the result of the authentication to OpenStack's Identity service (Keystone) using SAML assertions. The SAML assertions are then mapped to keystone user groups, based on which, the authenticating user can access cloud resources using their federated AARC ID.
Workflow
| 1. | Access OpenStack's Dashboard (Horizon) at https://am02.pilots.aarc-project.eu/horizon | |
| 2. | Click Connect and select your Identity Provider from the discovery page (WAYF). You may select any of the following options:
| |
| 3. | Enter your login credentials to authenticate yourself with the IdP of your Home Organisation (e.g. Google) | |
| 4. | After successful authentication, you may be prompted by your Home Organisation to consent to the release of personal information to the EGI AAI Service Provider Proxy | |
| 5. | On the EGI AAI Consent about releasing personal information page, click Yes, continue to consent to the release of personal information to the EGI User Account Registry. If you select the Remember option, your browser will remember your choice unless you clear your cookies or restart the browser. | |
| 6. | If this is your first time logging in, you will be redirected to the AARC Pilot User Community Sign Up page after successful authentication. Alternatively, you may access the sign up page directly by visiting: | |
| 7. | Depending on the LoA and/or attributes released by your Home IdP, there are two sign up workflows:
| |
| 8. | On the registration form, click Review Terms and Conditions | |
| 9. | If you agree to the Terms of Use, select the I Agree option. Important: You will not be able to agree to the terms until you review them! | |
| 10. | Finally, click Submit to submit your request. Important: You will not be able to submit your request until you agree to the terms! | |
| 11. | After submitting your request, you will receive an email with a verification link in it. After you click that link, you'll be taken to the request confirmation page. | |
| 12. | After reviewing your request, click Confirm and re-authenticate yourself using the Identity Provider you selected in Step 2. | |
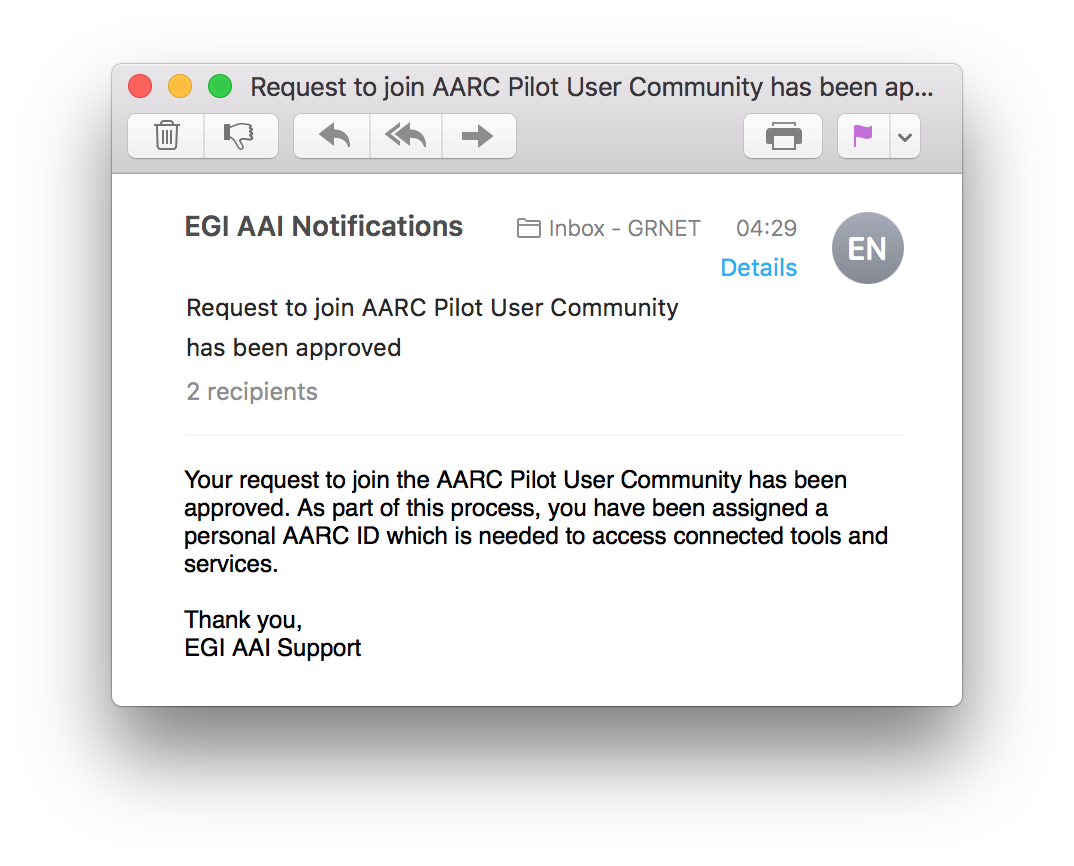
| 13. | If your sign up request requires approval (see Step 7), the Sponsor(s) of the VO will be notified via email. You will need to wait for a Sponsor to approve your request to join the AARC Pilot User Community. Upon approval, you will receive a notification email. | |
| 14. | After your registration has been completed, you can manage your profile through the Account Registry portal at https://aai-dev.egi.eu/registry | |
| 15. | Relogin to OpenStack's dashboard at https://am02.pilots.aarc-project.eu/horizon. You will be mapped to a Keystone user group based on the values of the eduPersonEntitlement attribute |
Components
- SimpleSAMLphp (version 1.14.5)
- simplesamlphp-module-openidconnect (commit affb54a)
- simplesamlphp-module-authfacebook (commit d8dc33c)
- simplesamlphp-module-authlinkedin (branch rc/authlinkedin)
- simplesamlphp-module-authorcid (master branch)
- COmanage Registry (version 1.0.4)
- Shibboleth (Service Provider version 2.5.3)
- Memcached (version 1.4.21)
- PostgreSQL (9.4)
- OpenStack