When GÉANT, as Data controller (DC), engage another organization as Data processor (DP) to process personal data on behalf of GÉANT, requirements defined in Article 28. of GDPR should be met and appropriate Data processing agreement (DPA) should be signed between GÉANT and DP.
Outline of DPA
Main part
Main part of DPA contains legal framework based on GDPR requirements which is common for all services. Regarding security of processing the following general security measures are defined:
- measures to ensure that the Personal Data can be accessed only by authorized personnel for the purposes set forth in Annex 2 of this Data Processing Agreement;
- In assessing the appropriate level of security account shall be taken in particular of all the risks that are presented by processing, for example from accidental or unlawful destruction, loss, or alteration, unauthorized or unlawful storage, processing, access or disclosure of Personal Data;
- the ability to ensure the ongoing confidentiality, integrity, availability and resilience of processing systems and services;
- measures to identify vulnerabilities with regard to the processing of Personal Data in systems used to provide services to the Data controller;
- measures to identify malicious activity or breach;
- measures to audit access control and privileges;
More specific security measures are defined in Annex 3.
Annex 1 - contact information
Contains contact information of DC's and DP's Data Protection Officers (DPO).
Example:
Contact information of the DPO <GÉANT's DPO name> of the Data controller. GÉANT Vereniging (Association) Hoekenrode 3, 1102BR Amsterdam, The Netherlands DPO (24x7) <GÉANT's DPO 24x7contact number> Contact information of the data protection officer of the Data processor. <Data processor's DPO contact information (address, phone, email…)> |
Annex 2 - list of personal data
Contains list of all personal data which will be processed and categories of Data subjects involved.
Example:
Personal data that will be processed for the purposes of providing technical support for the Service and solving technical problems.
Categories of data subjects: individuals from Research & Academia community using the Service. |
Annex 3 - specific security measures
Besides general security measures defined in main part of DPA, specific security measures which should be applied by DP in order to ensure protection of personal data can be defined. When properly implemented they can provide assurance that DP can provide adequate protection of rights of data subjects. These security measures are service specific and depends on architecture, scope and other factors. Risk assessment can be used to decide which measures should be implemented.
The following table shows some security measures, grouped be categories, which can be used as reminder. Chosen measures can be elaborated in more details in DPA, as appropriate. Table shows applicability of each security measure to different parts of data processor: organizational, system administration, network administration and application development. Which security measures and to which extend will be implemented is usually based on risk assessment. Table also shows which principle of Confidentiality, Integrity and Availability (CIA) of personal data is improved by each category of security measures.
Category with security measures | Organization | System admin. | Network admin. | Applications development | C | I | A |
|---|---|---|---|---|---|---|---|
| Security policy | |||||||
| achieved level n of GÉANT Security Baseline | |||||||
| appropriate security policy | |||||||
| Personnel management | |||||||
| personnel trained in (personal) data security | |||||||
| signed AUP or Statement of Confidentiality for (personal) data | |||||||
| Access management | |||||||
| role based access management | |||||||
| strong password or 2 factor authentication | |||||||
| logging of data modification | |||||||
| Access protection | |||||||
| network level (firewall, ACL, …) | |||||||
| server level | |||||||
| application or database level | |||||||
| Stored data protection | |||||||
| pseudonymisation | |||||||
| anonymisation | |||||||
| database encryption | |||||||
| hard disk and removable media encryption | |||||||
| other forms of data encryption | |||||||
| Data transfered protection | |||||||
| secure transport (IPsec, VPN, wireless, …) | |||||||
| secure remote system access (TLS, RDP, SSH, …) | |||||||
| secure remote application or database access (TLS, SSH, …) | |||||||
| Vulnerability management | |||||||
| timely patching | |||||||
| regular vulnerability scanning of applications or systems | |||||||
regular penetration testing of applications and systems | |||||||
| Malware protection | |||||||
| end-station malware protection | |||||||
| email malware protection | |||||||
| education of personnel | |||||||
| Data leak protection | |||||||
| IDS/IPS | |||||||
| SIEM or continuous monitoring | |||||||
| removable media policy | |||||||
| personnel education | |||||||
| Backups | |||||||
| backup policy ensure regular backups | |||||||
| stored on safe place | |||||||
| backed up data are encrypted | |||||||
| restore is regularly checked | |||||||
| Incident management | |||||||
| incident response procedure | |||||||
| timely reporting all incident to data controller | |||||||
| (D)DOS protection | |||||||
on network level | |||||||
| on system level | |||||||
| on application level | |||||||
Annex 4 - data transfers outside EU
Description of personal data transfers outside EU during processing.
Example:
Transfers to countries outside the European Economic Area without a suitable level of protection for which the Data controller has granted its authorisation: Not applicable. |
DPA approval procedure
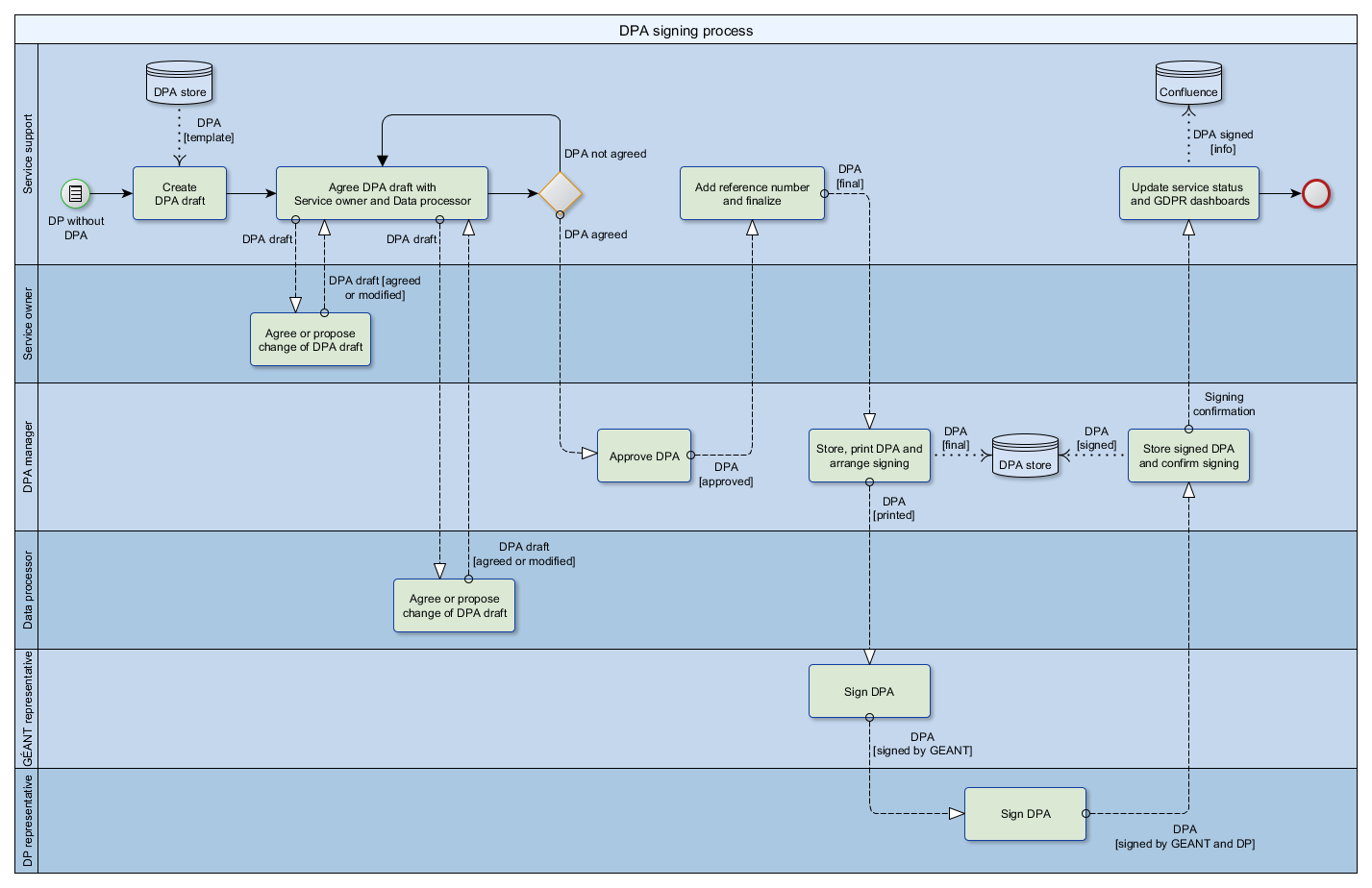
Process of drafting, approving and signing of DPA is shown on the following figure.
Roles and their activities
There are several roles involved in this process and each of them perform the following activities:
- Service support - WP5-T3.6 team which prepare agreed draft of DPA and update Confluence wiki.
- Service owner - owner of GÉANT's service.
- DPA manager - member of GÉANT, usually with legal background, who negotiates DPA with DP and approves final version.
- Data processor - representative of DP, usually with legal background, who negotiates and agrees with DPA proposed by GÉANT.
- GÉANT representative - representative of the GÉANT authorized to sign the DPA.
- DP representative - representative of the DP authorized to sign the DPA.